Research shows LLMs can conduct sophisticated attacks without human intervention
Discover how recent research indicates that Large Language Models (LLMs) can independently execute advanced cyberattacks, challenging current cybersecurity practices.
Discover how recent research indicates that Large Language Models (LLMs) can independently execute advanced cyberattacks, challenging current cybersecurity practices.
Discover key insights into the Philadelphia Indemnity Insurance data breach, its impact on consumers, and essential cybersecurity tips for protection.

Explore how the U.S. allegedly exploited a Microsoft flaw for cyberattacks against China, highlighting the intersection of cybersecurity and international politics.

Explore the nuanced role of cyber activities in the Israel-Iran conflict, revealing their limited impact amidst evolving warfare dynamics.

Explore crucial strategies for enhancing cybersecurity in healthcare. Learn how to protect patient data against evolving cyber threats effectively.
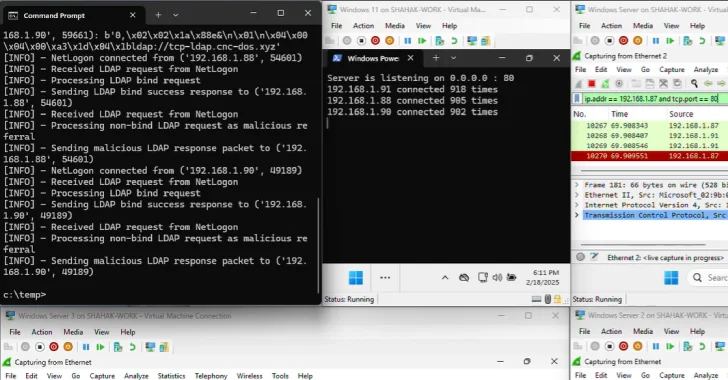
Discover new vulnerabilities in Windows Domain Controllers that threaten digital security. Learn how to protect your enterprise from potential DDoS attacks.

Stay updated on identity management and information security trends with our weekly summary. Discover key developments from August 1st to enhance your security strategies.
Explore how government agencies are spearheading quantum preparedness, essential for navigating the imminent technological shift impacting security and economies.

Discover the top malware removal software of 2025! This guide reviews the best options for effective, user-friendly protection against digital threats.

Explore the dynamic cybersecurity landscape and discover key stocks to watch for investment opportunities, ensuring your portfolio thrives in today's digital age.